For the first time, Bluetooth signals may be fingerprinted to monitor devices, according to a new study conducted by a group of scientists from the University of California, San Diego (and therefore, individuals).
At its heart, the identification is based on manufacturing flaws in Bluetooth chipset technology, which result in a “unique physical-layer fingerprint.”
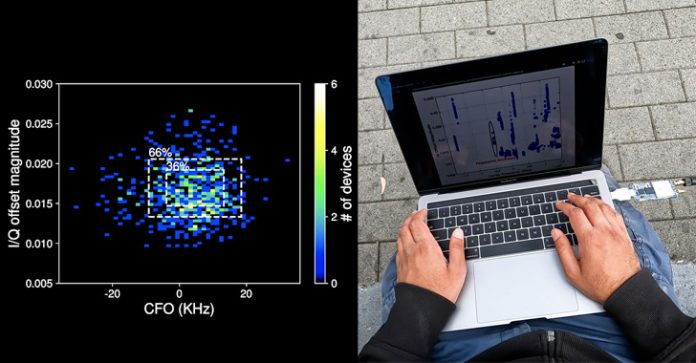
“An attacker must be equipped with a Software Defined Radio sniffer: a radio receiver capable of collecting raw IQ radio signals to undertake a physical-layer fingerprinting attack,” the researchers said in a recent article titled “Evaluating Physical-Layer BLE Location Tracking Attacks on Mobile Devices.”
The assault is conceivable because to the widespread use of Bluetooth Low Energy (BLE) beacons, which are constantly broadcast by current smartphones to allow critical tasks like contact tracking during public health situations.
The hardware flaws come from the fact that both Wi-Fi and BLE components are often combined onto a specialized “combo chip,” thereby exposing Bluetooth to the same set of metrics that may be used to uniquely fingerprint Wi-Fi devices: carrier frequency offset and IQ imbalance.
Extracting CFO and I/Q flaws for each packet using the Mahalanobis distance to assess “how similar the characteristics of the new packet” are to its previously recorded hardware imperfection fingerprint is the next step in fingerprinting and monitoring a device.
“Also, since BLE devices contain momentarily stable identifiers in their packets [i.e., MAC address], we may identify a device based on an average of numerous packets, enhancing identification accuracy,” the researchers said.
However, executing such an assault in a hostile environment presents numerous obstacles, the most significant of which is that the capacity to uniquely identify a device is dependent on the BLE chipset employed as well as the chipsets of other devices in close physical proximity to the target.
Device temperature, changes in BLE transmit power across iPhone and Android devices, and the quality of the sniffer radio utilized by the malicious actor to carry out the fingerprinting assaults are all important elements that might influence the findings.
“By evaluating the practicality of this attack in the field, particularly in busy settings like coffee shops, we discovered that while some devices have unique fingerprints and are thus particularly vulnerable to tracking attacks, others have common fingerprints and are frequently misidentified,” the researchers concluded.
“For mobile devices, BLE may be used to track their position. The ability of an attacker to follow a specific target, on the other hand, is mostly dependent on chance.”